ruben@rubenlabrada.com
P: (786) 873 - 7760
WHAT I DO

PROJECT MANAGEMENT
SYSTEMS ADMINISTRATION
Manage, coordinate, and develop project plans for private and government entities.
Windows, Linux, Mac OSX Server and desktop systems. If you use some obscure system I'd love to hear about it!
TECHNICAL SOLUTIONS
NETWORK SECURITY
Design and implement solutions that increase productivity and help your company grow.
Optimize network security, create security policies, and monitor your devices.
TECHNICAL SOLUTIONS
In order to stay competitive in the 21st century companies have to leverage every tool they can get their hands on. Don't gamble with your outdated infrastructure, it could cost you more money in the long run with unexpected downtime and inefficient systems. Servers need to be constantly maintained and upgraded, as robust as hardware and software have become, older systems become unstable, unreliable, and insecure, eventually leading to downtime and a severe reduction in efficiency.
CLOUD SERVICES
ON-PREMISE INFRASTRUCTURE
With Microsoft Azure, Amazon AWS, and other cloud services becoming more and more popular, should you consider moving to the cloud? Which service is right for you?
Chances are you have servers and network devices sitting in your office. Are you utilizing them to their maximum potential? Is your network experiencing slowdowns and your server just not cutting it anymore?
SKILLS

90%

99%
PROBLEM SOLVER
LEADER

75%

75%
SCRIPTING AND AUTOMATING
NETWORK/SYSTEM ADMINISTRATOR
COMMON PROJECTS
CLOUD MIGRATIONS
NETWORK OPTIMIZATION
AUTOMATION
NETWORK SECURITY
BACKUP SOLUTIONS

From small companies getting rid of their SBS server to large companies migrating dozens of servers, I've helped clients become more efficient and scalable by moving them to the cloud. Whether it's Microsoft Azure, Amazon AWS, or any other cloud solution, I'll help you review your options, plan the project, and help you execute the migration. In order to make the process as smooth as possible, you need to know what challenges lie ahead and run sufficient testing prior to starting the migration, contact me and I'll help you make the best decision for your business.

As companies grow, their networks need to expand with them and in many cases old hardware continues to be used with new systems. The dangers here are that this old hardware usually creates a bottleneck that ends up creating issues further down the line. When an expansion is in order, it is imperative to your business that you consider whether or not your current hardware will support the new devices. I can't stress enough the importance of getting a network audit completed prior to any upgrades or expansions being completed or else you risk running into network slowdowns or even unexpected downtime due to old wiring, outdated/failing switches, or even ill-performing and overextended routers.
Wireless access points, routers, switches, phones, and computers are all part of regular networks. Each device communicates with the outside world at an alarming rate and without preparedness your users could run into trouble. Networks need to be optimized, segmented, and QoS needs to be applied to allow certain devices to have a constant bandwidth so as to not cause issues such as choppy or inaudible calls with VoIP phones.

The 21st century has brought with it an incredible ability to automate tasks, that is, the ability to perform rigorous, tedious, and repetitive at the push of a button or on a schedule. Monitoring, patching, application deployments, and even server farm scaling can all be automated in this day and age. Remember that time is money and less time spent having to conduct these processes manually, means more time spent taking care of other problems.
A perfect example of this is a project I completed for 13 remote charter schools I was working with several years ago. Schools tend to be difficult for IT persons to manage due to the vast number of faculty members and students, in many cases repairing or imaging a computer is a manual process that could take up a technician's entire day.
In order to make it easier for my team and I to manage, I built an automated imaging server that during the computer's boot-up process checked if it had to be imaged. When a machine began acting up, I would issue the server a command and the machine would automatically reboot and image itself, it would then add itself back into the domain, install and activate any programs it needed, and even notified me when the process completed. This entire process was so efficient that it only took 15 minutes before the computer was fully operational again. Entire computer labs could be done overnight.

Security is a huge concern for larger companies but a security breach can be just as devastating, if not more so, to smaller companies. Ransomeware, Trojans, and hackers, are just some of the most common security issues that companies are having to deal with on a daily basis and if you are not properly protected, you could fall prey to the attacks.
While not every company needs the security of encrypted disks or emails, network security like firewalls are a must in this day and age. In many cases, one can't distinguish the difference between a mis-configured firewall and a cheap firewall incapable of preventing an attack. It has been my experience that the vast majority of firewalls are purposely mis-configured leading to holes in the firewall, all for the sake of ease of use and so as to not have to troubleshoot or take the time to configure the device properly. This is unacceptable and could lead to complete system compromise if left unchecked.
One of my most recent projects has been deploying 802.1X to an entire government contracted company. 802.1X is port-based Network Access Control (PNAC) and basically all it is, is a requirement for all devices connecting to a network, in this case both wireless and local networks, to authenticate before being given access to the network. Most modern devices such as phones, switches, routers, desktops, and devices are all capable of 802.1X. As this configuration called for all devices to authenticate, anything that plugs into the network or connected to company WiFi had to have been assigned a certificate that the RADIUS server could then authenticate. Now, if someone were to sneak into the facility and try to connect to the network, they would end up unable to access anything as they would not have a certificate, whilst the phones, desktops, and laptops that were permitted could access the network without compromise.
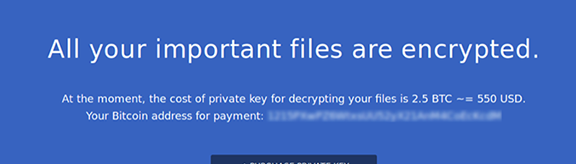
Imagine if you came into your office one day and you went to open the file you've been tirelessly working on the past couple weeks, only to be greeted with an error message and an empty document. You try another file, the same thing happens. Suddenly, you get a pop up message notifying you that your data has been taken hostage, you must pay a $5000 ransom in the hopes that the hackers will restore your data. You try accessing your files share only to realize that it has been compromised too. "No problem", you say to yourself, "I've got backups." You pull up your backup server and to your horror realize that the last backup was three weeks ago. A sinking feeling sets in as you begin to panic. What now?
In the past year alone I have heard of 5 of my colleagues running into this same issue. Unfortunately there is no telling if you will be able to recover your data by paying, so it is often better to just cut your losses and go back to your last backup. And if you don't have any backups, well that can be a very, very devastating blow to your company and possibly clients.
